by Dennis Crouch
Western Digital Techs., Inc. v. Viasat, Inc., No. 22-CV-04376-HSG, 2023 WL 7739816 (N.D. Cal. Nov. 15, 2023) Docket No. 4_22-cv-04376
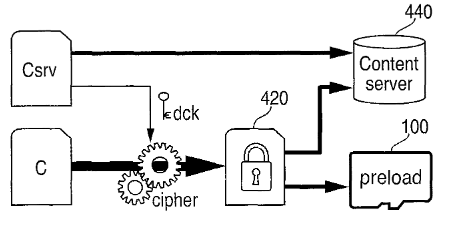
Western Digital sued Viasat for infringing claims from several patents, including US8,504,834, which covers “media streaming systems and software.” In a recent decision, Judge Haywood (N.D.Cal.) granted a motion to dismiss — finding the claims of the ‘834 patent directed to ineligible subject matter. The background section of the patent explains explains that prior art systems decrypted locally stored content using a decryption key obtained from a digital rights management (DRM) server. This had drawbacks related to efficiency and cost. The patent describes an improved system where the decryption key is derived from a stream of data received over a network, rather than needing to contact a DRM server.
Claim 14, treated by the court as representative, recites:
A method for activation of local content, the method comprising:
performing the following in a host device in communication with a storage device storing encrypted content:
receiving a stream of data from a network;
deriving a key from the received stream of data; and
decrypting the encrypted content using the key derived from the received stream of data.
The claim covers a method for decrypting locally stored encrypted content. A host device receives a stream of data over a network, derives an encryption key from that stream, and uses that derived key to decrypt encrypted content stored on a connected storage device.
Alice Step One – Is the Claim Directed to an Abstract Idea?
At Alice step one, the court asks whether the claim is “directed to” a patent ineligible abstract idea. Here, the court found claim 14 is directed to the abstract idea of “delivering and deriving a decryption key from a stream of data.” The court provided several bases for deriving this idea as gist of the claim and for concluding that it constitutes an abstract idea.
First, the court analyzed the focus of the claimed advance over prior art systems as described in the patent background and specification. The court found the focus was on using a stream of data to deliver and derive a decryption key, rather than contacting a DRM server.
The court then noted that the claims are functional in nature — claiming the result itself. On this point, the court found that claim 14 does not recite any practical method of implementation, but rather uses only generic computer components like a “host device” and “network” along with conventional processes like “receiving,” “deriving,” and “decrypting” to achieve the result. This demonstrated the claim was drafted in a result-oriented or functional manner focused on the principle itself.
The court also found that the key steps of claim 14 could be performed by a human mind or with pen and paper by deriving a decryption key from a received communication and using it to decrypt content. This indicated abstraction under Federal Circuit precedent.
Finally, the court analogized the claim to those found abstract in several other cases, where claims merely collected, organized, transmitted data without a specific new process for doing so, including Electric Power Group, LLC v. Alstom S.A., 830 F.3d 1350 (Fed. Cir. 2016) (collection, analysis, and display of data are abstract), and Two-Way Media Ltd. v. Comcast Cable Commc’ns, LLC, 874 F.3d 1329 (Fed. Cir. 2017) (broad functional steps that lacked technical details were abstract).
Alice Step Two – Does the Claim Recite an Inventive Concept beyond the Abstract Idea itself?
At step two of Alice, the court searches for an inventive concept to ensure the claim amounts to significantly more than the abstract idea. Here, the court found no inventive concept in claim 14, when considered either element-by-element or as an ordered combination.
The court found that the claim elements recite only generic computer components like a “host device” performing conventional computer functions like “receiving” and “deriving.” Plaintiffs apparently did not dispute this.
For the ordered combination, Plaintiffs argued that using streaming data to provide decryption keys in the claimed manner was unconventional and advantageous over prior systems. But the court rejected this, finding that any such unconventional use or improvement described in the specification was untethered from the broad claim language. The court held that even assuming the specification discloses specific steps rendering use of streams unconventional, those details are missing from claim 14.
Conclusion
Because this was at the motion to dismiss stage, the Court permitted Plaintiffs leave to amend their infringement allegations related — perhaps to include factual allegations that show eligibility. However, the patentee subsequently provided the court with notice that it will not be filing an amended complaint.
While Plaintiffs respectfully disagree with the Court’s determination under 35 U.S.C. § 101 for all of the reasons set forth in its briefing on the issue (see, e.g., Dkt. No. 53), Plaintiffs are not filing an amended complaint and instead reserve the right to appeal the Court’s decision when final judgment is entered in this case.
P’s Response to the Court’s Order. The case is ongoing with two additional Western Digital patents — each which contain claims with more technological detail imbedded into the claims. The outcome here recognizes that patentees are finding ways to overcome the eligibility issues, both at the PTO and in court, but there are still lots of traps. Though workarounds now often exist, Alice/Mayo still present ample opportunities to find claims abstract – particularly for computer-implemented inventions. The path forward for Plaintiffs remains challenging despite their arguments on appealability.